Free vs Paid Cyber Security Training: The Secret to Career Success

Training is vital for success in cybersecurity. Let's explore the options you have at your disposal and perhaps the best path to follow to achieve your goals.
We use cookies to help you navigate efficiently and perform certain functions. You will find detailed information about all cookies under each consent category below.
The cookies that are categorized as "Necessary" are stored on your browser as they are essential for enabling the basic functionalities of the site. ...
Necessary cookies are required to enable the basic features of this site, such as providing secure log-in or adjusting your consent preferences. These cookies do not store any personally identifiable data.
Functional cookies help perform certain functionalities like sharing the content of the website on social media platforms, collecting feedback, and other third-party features.
Analytical cookies are used to understand how visitors interact with the website. These cookies help provide information on metrics such as the number of visitors, bounce rate, traffic source, etc.
Performance cookies are used to understand and analyze the key performance indexes of the website which helps in delivering a better user experience for the visitors.
Advertisement cookies are used to provide visitors with customized advertisements based on the pages you visited previously and to analyze the effectiveness of the ad campaigns.

Training is vital for success in cybersecurity. Let's explore the options you have at your disposal and perhaps the best path to follow to achieve your goals.

Learn how attackers use the Windows Startup Folder to maintain persistence once they’ve compromised a machine. Then hunt for these malicious Startup Folder items.

Discover how to create your own custom Sigma rules to hunt for the latest threats that are affecting your environment and thwart threat actors.

Learn how attackers use Windows services to maintain persistence once they’ve compromised a machine. Then see how to hunt for these malicious services.

Learn how to use threat intelligence articles, the MITRE ATT&CK framework, and Sigma rules to perform threat-informed hunting using Splunk queries.

Learn how attackers use scheduled tasks to maintain persistence once they’ve compromised a machine. Then see how to hunt for these tasks.
Let's explore the MITRE ATT&CK framework and find out why it's a must know tool for any cyber threat intelligence analyst looking to tackle the latest threats.

Learn how attackers use Windows registry keys to maintain persistence once they’ve compromised a machine. Then see how to hunt for these malicious keys.
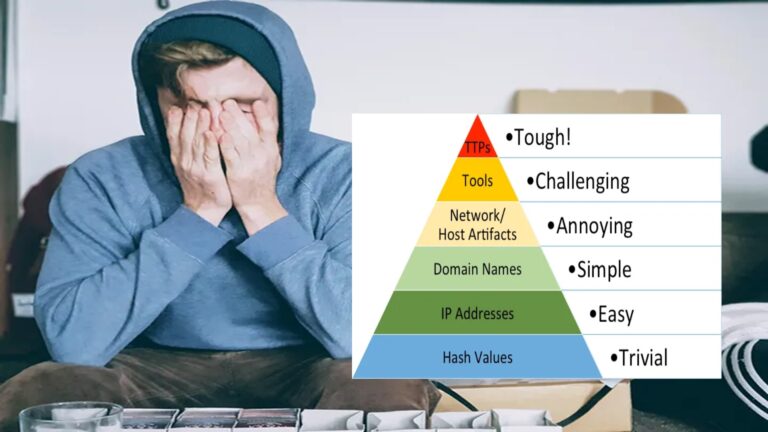
Discover how to turn a bad guy's day into a nightmare using the Pyramid of Pain to elevate your threat detections and increase the cost on adversaries.

Whodunit is a tool that can be used to identify the most likely Advanced Persistent Threat group responsible for an attack. Let's find out how to use it!

Learn how to use Velociraptor’s threat hunting capabilities to identify malicious activity associated with real-world malware and threat actors in this demo.

Discover how to create a virtualized threat hunting environment and use Velociraptor as a threat hunting tool to sniff out malicious reverse shells.
Learn what threats are, what threat hunting is, and the basic security requirements needed to start a threat hunting program in this series introduction.
Learn how to create a safe and secure malware analysis environment that is tailored towards your analysis needs using the power of virtualization.
Discover the power of virtualization and how to create your own home lab environment for malware analysis, threat hunting, and software development.