All cyber threat intelligence teams need three things: a threat intelligence lifecycle, a threat model, and intelligence requirements. One of the hardest to get right is intelligence requirements. They usually lack focus, fail to define a timeframe, or do not answer a single question to support an informed decision. But what are the challenges when creating intelligence requirements, and how do you overcome them?
This article dives into the top five challenges you will face when creating your own intelligence requirements so you can avoid these pitfalls and produce actionable intelligence that is valuable to your organization. You will learn about common real-world problems that come with implementing intelligence requirements and solutions to navigate past these issues.
But, before we begin, let’s first recap what intelligence requirements are.
Intelligence Requirements Recap
Intelligence is the information you collect about a competitive entity, usually an adversary, and how they may affect your organization. You use this information to discover the best way to defend yourself.
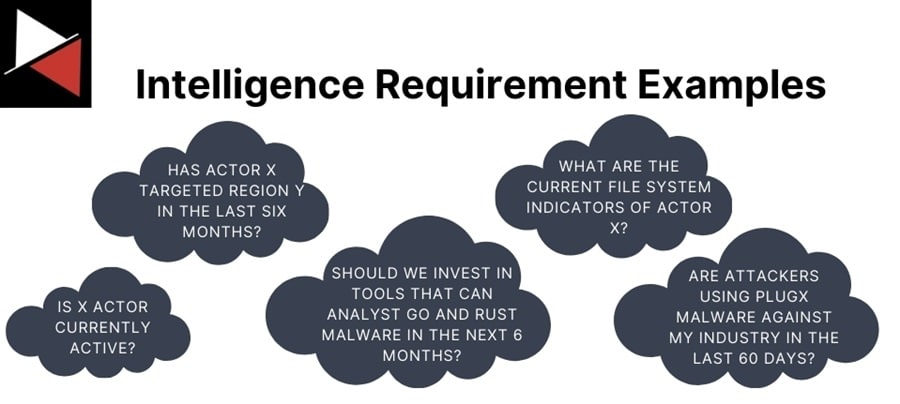
Intelligence requirements are the insights you seek to gain, the questions you want answers to, and the signposts that guide your intelligence work. They should aim to address a knowledge gap and inform action by being simple, focused, and supporting a single decision that a stakeholder needs to make. This may be a technical decision made by your security operations team or a strategic decision made by an executive.
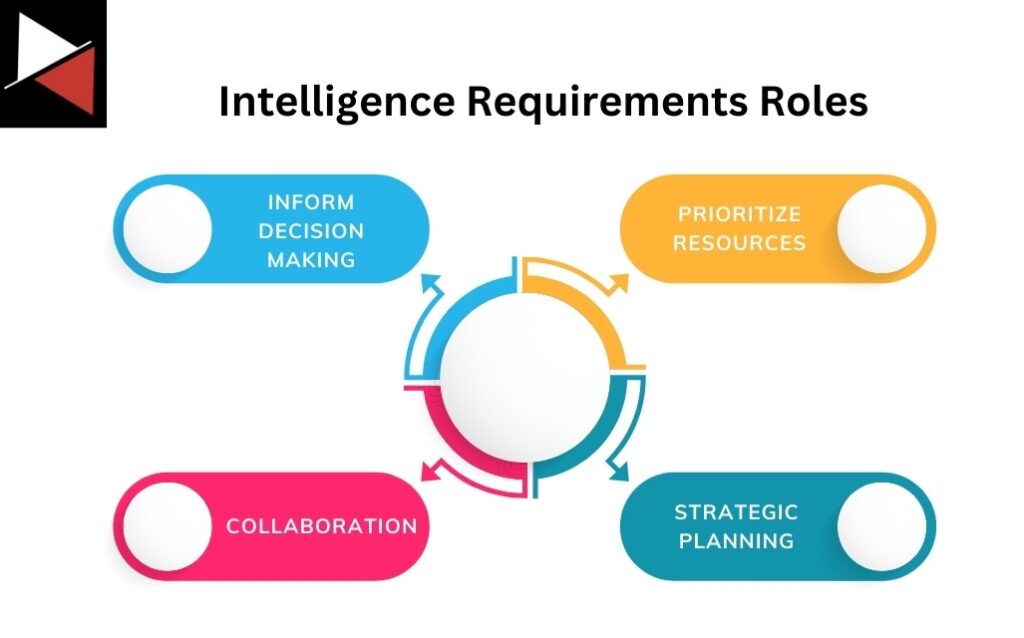
Here are the key roles intelligence requirements play:
- Inform decision-making: Intelligence requirements fill a knowledge gap, enabling a stakeholder to make an informed decision backed by data. This minimizes uncertainty and ambiguity, pathing the way for action.
- Prioritize resource allocation and efforts: By filling a knowledge gap, intelligence requirements allow you to allocate resources and your team’s efforts effectively. They highlight the threats you can defend against while showing what you need to invest in to defend the ones you cannot.
- Support strategic planning: Intelligence requirements can be used to gain insight into how the threat landscape evolves over time, helping you plan your investments and defense strategies to combat emerging threats.
- Enable collaboration and cohesion: Good intelligence requirements demand collaboration between the intelligence producer and consumer. You must have strong lines of communication among your security teams to create and fulfill intelligence requirements. This forces teams in your organization to collaborate and act cohesively, improving security overall.
If you want to learn more about intelligence requirements and how to create them, read What Are Intelligence Requirements? A Comprehensive Guide.
Challenges When Creating Intelligence Requirements
Now you have a basic understanding of what intelligence requirements are and the role they play. It’s now time to sit down and write your own. You soon realize your threats are constantly changing, you have limited resources to perform your intelligence work, and you are swimming in a sea of information you don’t know how to navigate. Welcome to the world of Cyber Threat Intelligence (CTI).
Let’s discuss some of these and the solutions you can use to overcome these challenges.
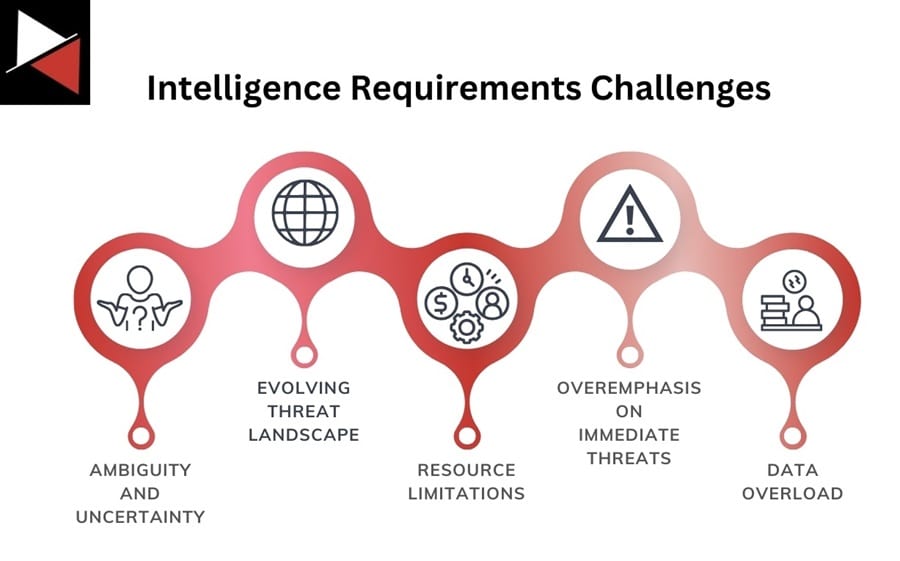
Ambiguity and Uncertainty
Often you won’t know what or how intelligence might help a certain team. Despite spending hours brainstorming ideas and modeling threats, you still cannot come up with any use cases that could be enhanced with intelligence. However, the only thing worse than spending time brainstorming is trying to implement an intelligence requirement with no value. So what’s the solution?
Solution
The only way to find out what a team needs is to ask them. Ask the team you are generating intelligence for about their pain points, common problems they need to solve, or workflows. Once you understand how a team does its job, use your experience to identify how intelligence might help them. Spend a week or two walking in their shoes, you will soon find out what they need so they can do their job better.
This is considerably easier for security-focused teams, but try to step outside your comfort zone and explore how intelligence can help non-security-focused teams. Information can help everyone make better decisions.
The Evolving Threat Landscape
Every day it seems like a new threat is emerging. A new threat actor attacks a major business, a new piece of malware is discovered, or an exploit is found in the wild. Threats change over time. You must adapt to these evolving threats and adjust your intelligence requirements to reflect these changes. That said, it is important not to change your intelligence requirements constantly. This will only overload you with information and diminish your team’s capabilities. So what intelligence requirements should you create?
Solution
Create two types of intelligence requirements. Create General Intelligence Requirements (GIRs) that will hold true for a long period of time and will be an ongoing requirement of the intelligence consumer you support. While also creating Priority Intelligence Requirements (PIRs) for new and emerging threats. These should be tied to specific events or a time period and fulfilled immediately. Once fulfilled, you can throw them away to reduce your workload.
Resource Limitations
Resource limitations constrain all teams and will limit the number of intelligence requirements you can fulfill. These limitations may exist in the technology, people, or processes used. Fixing technology or people issues can be difficult because they require investment and buy-in from management, such as buying tools, increasing log capacity, or hiring new employees. Instead, focus on processes.
Solution
The easiest limitation to tackle is processes. You can always strive to optimize your CTI team’s processes because they are a resource that falls most under your control. Explore new ways of doing things, measure their effectiveness, and consult with employees in and outside your company about the best way to do things. Optimizing your processes, procedures, and workflows should be your number one priority.
Overemphasis on Immediate Threats
Many security operations teams will want you to focus on immediate and present dangers. Their work revolves around defending the front line from cyber attacks, and they will want operational intelligence they can use immediately. Don’t fall into the trap of only writing intelligence requirements focusing on immediate threats!
Solution
Work with the security operations team to create well-rounded intelligence requirements, including operational, tactical, and strategic requirements. You want to produce intelligence for the security operations team that they can use to combat threats at a higher level through better security architecture and more effective passive defense that doesn’t require constant human interaction. Look at Elevate Your Threat Detections Using the Almighty Pyramid of Pain for more details.
Data Overload
Once you tell people you are creating intelligence requirements, you will soon discover everyone wants onboard. They will treat intelligence requirements as the latest deal at Walmart (or Tesco) and try to get as many as possible! If you try to fulfill all the requests for intelligence requirements you receive, you will soon be overwhelmed with the data you need to process through your Threat Intelligence Lifecycle.
Solution
To overcome having too many requirements, try to group similar needs into one intelligence requirement that you adapt to your audience during the Dissemination phase. For instance, the SOC and incident response team may have some operational intelligence requirements, like indicators related to threat actor XYZ. If you can group intelligence requirements, it reduces the heavy lifting your CTI teams have to do, reducing the data you have to sift through to find answers.
You can also map data sources to intelligence requirements as you create them. Using a Collection Management Framework (CMF) that details where to find data to answer specific questions. This will save you from aimlessly trawling through irrelevant data and becoming overwhelmed. We will look at CMFs later in this series.
Conclusion
Intelligence requirements are hard to get right. You will often face various challenges when creating and implementing your own, from ambiguity and uncertainty about how intelligence can benefit a certain team to having too many requirements to fill.
The solutions detailed in this article to overcome these challenges can be boiled down to three main things:
- Communication: Clear communication with your intelligence consumer will help you understand their problems and generate use cases for intelligence that bring them value.
- Focusing on the bigger picture: Not getting caught up in the constant barrage of new threats or intelligence requests will help your team stay on course and focus on requirements that bring value. Use PIRs and GIRs to prioritize your intelligence work.
- Practice and refinement: No one gets it right on their first go. Practice writing intelligence requirements, see what works, and refine them to ensure they continue to deliver value.
Focusing on these three keys is vital to overcoming the challenges associated with intelligence requirements and CTI in general. They will steer you clear of doing intelligence for intelligence’s sake and bring real value to your organization.
Frequently Asked Questions
What Are Intelligence Requirements?
An intelligence requirement is simply a knowledge gap that needs answering to support a single decision that a key stakeholder needs to make. This could be an operational decision, such as what TTPs to focus on, or a strategic decision, like what security tools to invest in over the next two years. Intelligence requirements should be simple, focused, and support a single decision.
Why is Defining Intelligence Requirements Challenging?
Intelligence requirements are difficult to define for a number of reasons. Some reasons are ambiguity and uncertainty, the evolving threat landscape, resource limitation, overemphasis on immediate threats, and data overload. However, by implementing the solutions detailed in this article and practicing creating and refining your own requirements, you will soon master them!
How to Create Intelligence Requirements?
Intelligence requirements can be created in three simple steps:
- Determine who the consumer of your intelligence is. This could be technical teams like security operations or incident response, non-technical teams like branding and marketing, or even executives.
- Identify the knowledge gaps that need to be filled for them, such as pain points or use cases that can be enhanced with intelligence.
- Refined these knowledge gaps into intelligence requirements so that they focus on a specific fact, event, or activity and answer a question that supports a single decision.
To learn more about how to create intelligence requirements, read this comprehensive guide.



