Free Learning Resources
Cyber Threat Intelligence
Our cyber threat intelligence content contains unique insights from industry experts, threat intelligence theory to help you understand complex topics, and practical use cases you can implement at your company to enhance its cyber security posture.
5 Mistakes I Made as a New Cyber Threat Intelligence Analyst

Top 5 Challenges When Creating Intelligence Requirements

Threat Intelligence with MISP: Part 2 – Setting up MISP
Discover the Ultimate Cyber Security Notetaking App: Polarity

Threat Intelligence with MISP Part 6 – Using the API

5 Cyber Kill Chain Challenges and How to Prevail

Intelligence Requirements Template (PDF + Word Doc Download)
The Traffic Light Protocol: How to Classify Cyber Threat Intelligence

Top 5 Challenges With Indicators and How to Overcome Them
Threat Hunting
Our threat hunting content will help you master the mysterious art of hunting down threats in the cyber realm.
You will see how to create complex hunting queries, automate your threat hunting workflow, and create your own hunting tools.
Python Threat Hunting Tools: Part 10 — The Power of Jupyter Notebooks
MITRE ATT&CK Framework: Holy Bible of Threat Intelligence

Elevate Your Threat Detections Using the Almighty Pyramid of Pain

Python Threat Hunting Tools: Part 2 — Web Scraping

Threat Hunting With Velociraptor I – Introduction

Python Threat Hunting Tools Part 6 — Creating EXEs from Python Files

How to Arm Yourself with Custom Sigma Rules

Python Threat Hunting Tools Part 7 — Parsing CSV

Threat Hunting With Velociraptor III – Hunting Demo
Custom Tooling
Our custom tooling series will empower you with the superhuman powers programming and scripting can deliver.
You will learn how to create testing environments, use various languages to build your custom tools, and make your workflows more efficient with automation.

Python Threat Hunting Tools Part 6 — Creating EXEs from Python Files

Python Threat Hunting Tools: Part 9 — Creating Python Packages with Poetry

Let Us Find Out Whodunit
How to Create a Home Lab: Virtualize all the Things!

How to Automatically Deploy a Malware Analysis Environment

Python Threat Hunting Tools: Part 1 — Why?
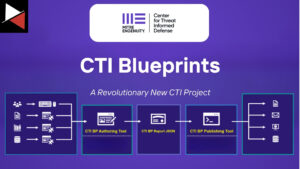
Discover MITRE’s CTI Blueprints: A Revolutionary New Project

Creating Your Own CTI Aggregator for Free: A Complete Guide

Python Threat Hunting Tools: Part 11 – A Jupyter Notebook for MISP
Stay up-to-date whenever we release articles, tips, and guided tutorials. Don’t miss a thing and signup to get notified of new content.
Thank you!
You have successfully joined our subscriber list.
